Who can add blocks to the Blockchain, how, why & when? [Consensus algorithms]
Adding new blocks on the blockchain, how it is done, by whom and when
Table of contents
- Refresher
- Gate Keepers [Miners]
- Back story of miners
- Chronology (When miners are needed)
- Rewards :
- Why We Need a Consensus Algorithm
- What is a Blockchain Consensus Algorithm:
- Single Truth
- Attacking Bitcoin (educational purposes only)
- Types of Consensus algorithms (most popular)
- Proof-of-Work (PoW)
- Proof-of-Stake (PoS)
- Proof-of-History (PoH)
- Proof-of-Authority (PoA)
- Proof-of-Reputation (PoR)
In this article, I've tried to simplify the concept of adding new blocks on the blockchain, how it is done, by whom and when, is there a person/group sitting all day on their computers adding blocks that they like, is adding new blocks an arbitrary process?
I'll make a small refresher and then dive into the subject, you will find more resources at the end of this article if you wanted to learn more.
Refresher
One of the blockchain promises are, Transparency, traceability, immutability, and security it achieves this by a smart way of encryption its transactions ( Merkle Tree ) and linking data (blocks) The idea after this is to link blocks in a way that Each block has in it the Hash of the previous block ..Etc, the hash is of each block is a Hexadecimal string generated from all the transactions of a given block
The trick is for example we had 10 blocks in the blockchain if an attacker tries somehow to change block number 5, the hash will change and all the blocks after block 5 will be invalidated because each of them is linked by the previous block hash and so, this attacker's request to change will be defended by the miners
Gate Keepers [Miners]

As pivotal as it is, only a few understand how such a dynamic conception works in practice; and among the most ignored aspects include just how new blocks on the blockchain are securely added to the ledger, considering no centralized authority is engaged to maintain the integrity of the network.
The gatekeepers of the blockchain are simply , the miners , But who are miners , why we need them and what they gain ?
Back story of miners
Why Do blockchain Need miners (case of cryptocurrency)
Because blockchain is entirely digital records, there is a risk of copying, counterfeiting, or double-spending the same coin more than once. Mining solves these problems by making it extremely expensive and resource-intensive to try to do one of these things or otherwise "hack" the network. Indeed, it is far more cost-effective to join the network as a miner than to try to undermine it.
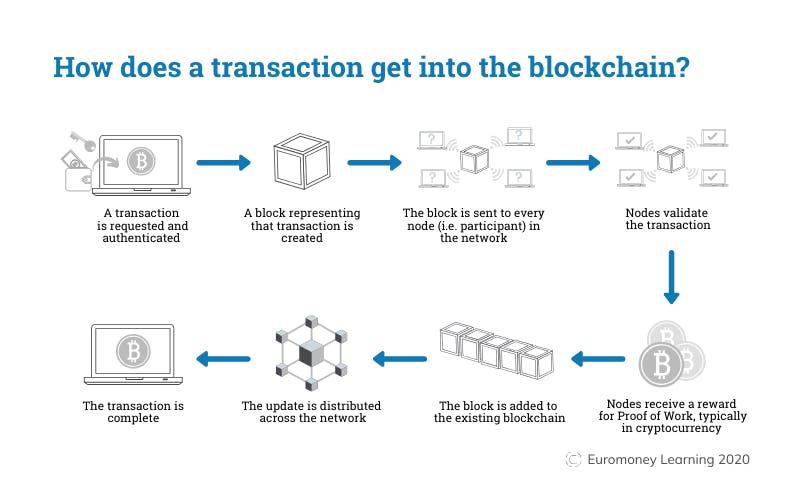
Every node that participates in the blockchain network as a miner (Which has the official mining software) runs a mathematical operation and performs a series of checks to validate the transaction for correctness.
They check all the parameters in consideration are valid. For example, nonces of the concerned transaction should not be exceeding the length of the block, which is pre-defined as a rule in the blockchain.
If any node successfully validates the correctness of the transaction this transaction becomes a part of a new block and is broadcasted across the blockchain network of nodes. After everyone in the node approves that yes transactions exists, then only the transaction goes through successfully, and a new block becomes a part of the legacy bitcoin blockchain.
Chronology (When miners are needed)
let's take this example: Lets say you have 5 Bitcoins, you want to send 1 Bitcoin to your friend Step 1 : You open your wallet Step 2: You got to send screen Step 3: You Enter your friend Bitcoin Address and amount Step 4 : You tap Send
Now your role as a Bitcoin Blockchain user end
Step 5 : your wallet app will broadcast this transaction to the bitcoin network Step 6 : now your transaction is pending to be picked up by miners and verified Step 7 : once your transaction has been pickedup , the miner software will start verifying your transaction , do you have enough balance , they will also take the Signature Script and run it with the PubKey Script Step 8 : if verification is successful the miner will broadcast a confirmation to the network , if not it won't
Rewards :
As you may have guessed mining is not a non-profit act , miners make big hardware investments and they expect to be rewarded for successful block mining. Miners get back. But it is not as straightforward as it sounds. The value of rewards depends upon the capacity and quality of mining hardware. The more power and hard work which gets into the mining process leads to higher rewards.
in the case of bitcoin, there are 2 types of rewards
New Bitcoins: currently On May 11, 2020, the reward halved again to 6.25 BTC per new bitcoin mined
Block reward : The miners who verify transactions are collectively known as validators / miners , but can also be called stakers or miners – depending on the consensus mechanism used by the blockchain (proof-of-stake or proof-of-work, respectively.)
What i just explained is how bitcoin consensus algorithm works, which is called Proof of Work (PoW) the consensus algorithms in blockchain are the rules or the mechanisms blocks are added to the blockchain
Let's understand what are the consensus algorithms in Blockchain
Why We Need a Consensus Algorithm
Satoshi Nakamoto proposed rules enforcing all nodes of a distributed network to agree on a single truth with absolute certainty. It added elements of game theory to avoid unethical participants of the system adding false transactions and blocks, by providing the correct incentives and penalizing dishonest participants. Without a consensus algorithm in Blockchain, we couldn’t agree which transactions and blocks need adding to the blockchain.
What is a Blockchain Consensus Algorithm:
A consensus algorithm is a process in CS used to achieve agreement on a single data value among distributed systems (in our case blockchain network & nodes) . Consensus algorithms are designed to achieve reliability in a network involving multiple nodes. Solving the issue of how we can get a single point of truth
Single Truth
In short , consensus algorithms have 2 goals:
1- Make sure that the next block in a blockchain is the one and only version of the truth (Single truth)
2- keeping powerful adversaries from derailing the system, and successfully forking the chain.
So Without a consensus algorithm in Blockchain, Miners' nodes (gatekeepers) can't agree on which transactions and blocks need to be added to the blockchain. Furthermore, without a consensus mechanism, every blockchain miner would have Different blocks & chains with different transactions, As result, it wouldn’t be a single truth
Attacking Bitcoin (educational purposes only)
lets imagine you want to attack The bitcoin network for some reason , what do you need to be able to attack the bitcoin network , you'll need to have more than 50% of the bitcoin network computational power , as of Feb 12, 2022 , the bitcoin computational power was 266.94 EH/s . EH stands for Exa hashes or 266 Quintillion hashes to put things into perspective 1 AntMiner S9 hashrate is currently top: 14,000 GHash/s
Meaning you'll need more than 15,2 million AntMiner S9 to reach 51% of today bitcoin hashrate , in today price assuming the AntMiner S9 price is 2,400 USD that'll cost you 36.5 billion USD not counting the electricity bill which will be astronomical aswell that'll be one expensive attack
Types of Consensus algorithms (most popular)
Since bitcoin inception , there has been couple of innovations in this regard , some blockchain companies has published different approaches than bitcoin PoW, resulted in more 84 Blockchain Consensus algorithms to this date
Proof-of-Work (PoW)
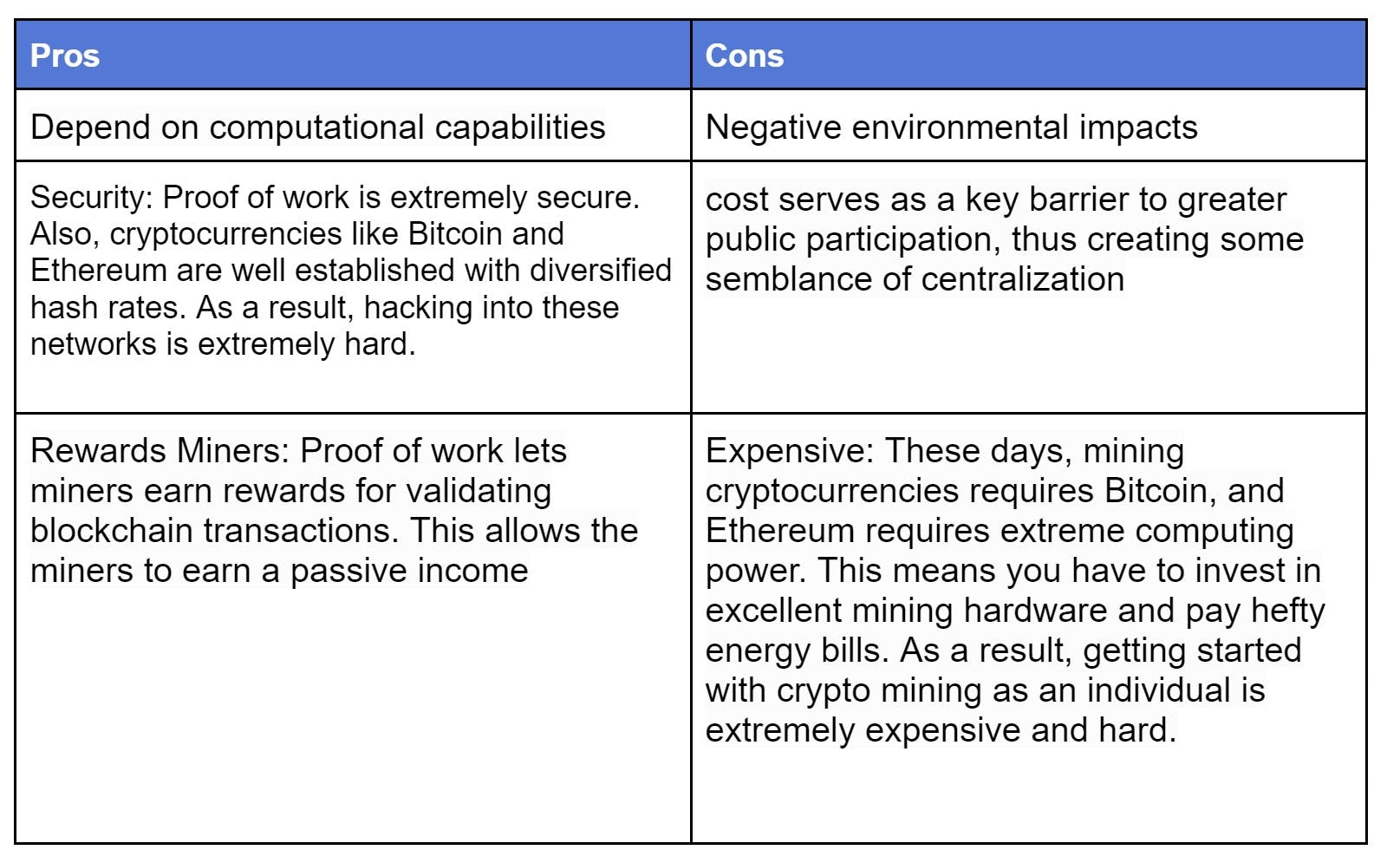
Proof-of-work is the first Blockchain consensus algorithm used by Satoshi Nakamoto's Bitcoin, this mechanism allows the blockchain network to come to a consensus, or agree on things like account balances and the order of transactions. This prevents users from "double spending" their coins and ensures that the Bitcoin Blockchain is tremendously difficult to attack or manipulate
Proof-of-Work requires nodes to compete against one another by solving a complex mathematical equation. It is done by repeatedly running a hashing algorithm until a solution to the equation is found. Then, other network nodes cross-check the solution to ensure its authenticity, Once the solution is found and verified by the network miners, the miner who solved the problem can create the new transactions block. The miner will also receive a reward for the computing work.
Proof-of-Stake (PoS)
Unlike PoW proof of work, where miners use computer processing power to validate transactions, proof-of-stake is an alternative that requires less power for transactions to be authorized. it works by granting block creation rights to network nodes with the highest account balance (or stake).
These nodes are referred to as validators. who stake more value have a higher probability of creating the next block. Meaning Any Validator with a significant stake in a blockchain has a vested interest in preserving the network’s integrity. In case of a malicious validator who tries to add fake transactions into the network, they could lose their stake
Today, the community looked to PoS as a possible replacement of Proof of work . The PoS approach does not require extensive computational power for mining. Hence, the process consumes significantly less electricity as result it is cleaner for the environment. Moreover, the PoS consensus can confirm transactions in much less time meaning it can have higher TPS (transactions per second), making it more efficient than PoW
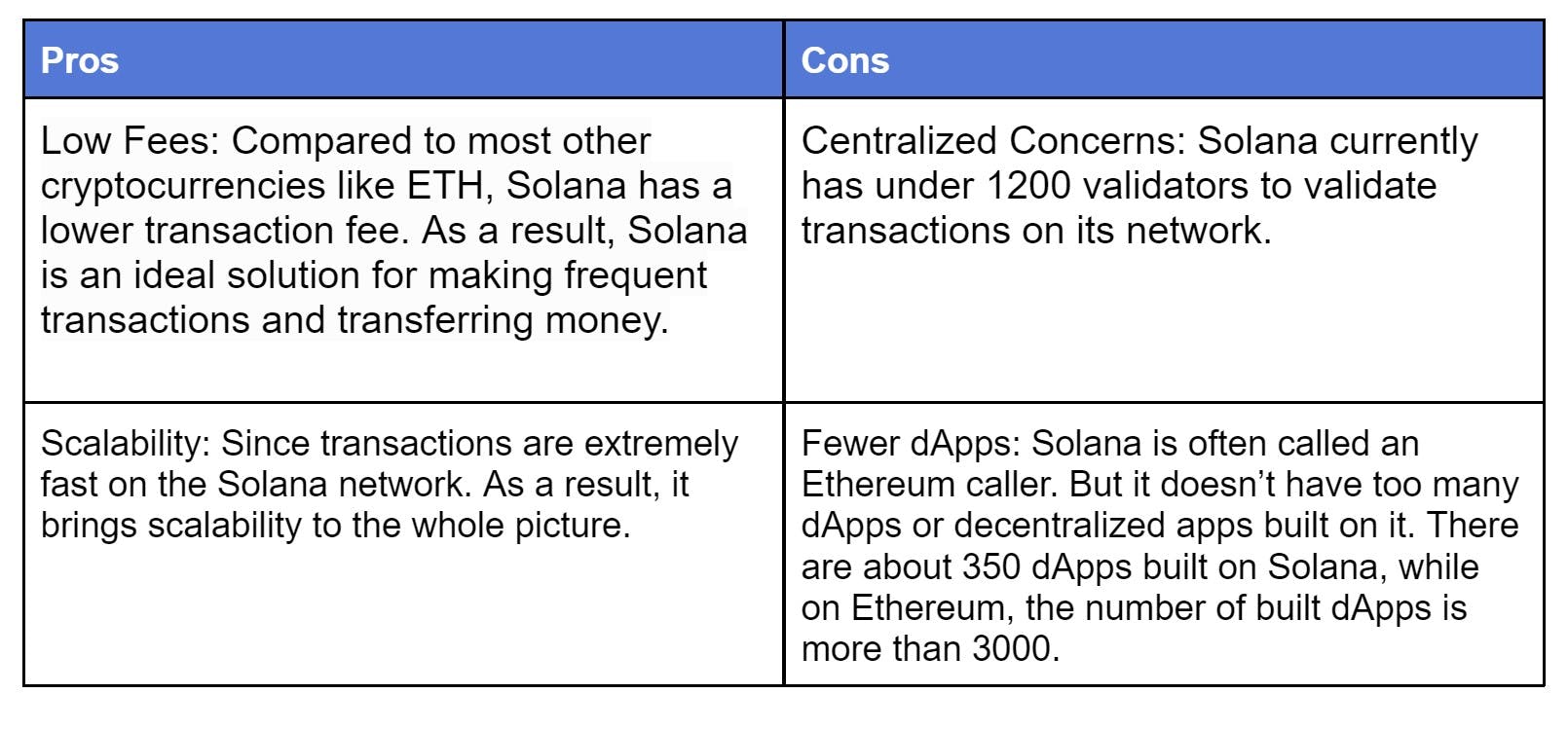
Proof-of-History (PoH)
This is One of my favorites consensus algorithms is PoH, Instead of relying on the transaction’s timestamp, PoH users can prove the transaction before or after a particular activity.
For instance, a user can capture the cover of the Washington Post as transaction proof. The newspaper’s publication date will confirm it.
The PoH can create historical evidence verifying that the event occurred at a specific point in time. It is a verifiable delay function with a high frequency. In PoH, the function requires a certain number of sequential steps to assess. These steps will prove the transaction’s authenticity. It then yields a unique output that can be efficiently and publically validated.
i recommend checking Solana explainer video about PoH : youtube.com/watch?v=rywOYfGu4EA
Proof-of-Authority (PoA)
Soon..
Proof-of-Reputation (PoR)
POR is an upgraded, stronger, and more secure form of Proof of Authority (POA) Algorithm. In POA the transactions and blocks are validated by approved accounts known as validators. POA has typically been used in private networks and most recently a few companies that have adopted it to use individuals as the validators whose identities are publicly disclosed and at stake.
if you want to check more check this amazing git , tokens-economy.gitbook.io/consensus
Thanks for reading , make sure to subscribe to this blog and newsletter so you wont miss any article

![Who can add blocks to the Blockchain, how, why & when? [Consensus algorithms]](https://cdn.hashnode.com/res/hashnode/image/upload/v1649289998326/7VHxIfY5i.png?w=1600&h=840&fit=crop&crop=entropy&auto=compress,format&format=webp)